Intune compliance policies define the rules a device must meet before it can access corporate resources. In a Zero Trust model, compliance is the baseline — a device that fails to meet your standards gets blocked from email, SharePoint, and Teams, regardless of whether the user has valid credentials. This guide explains how to create and assign Microsoft Intune compliance policies for Windows, macOS, and iOS devices.
Compliance policies work in tandem with Entra ID Conditional Access to enforce your security posture. Without a compliance policy, Intune marks all devices as not evaluated rather than compliant. See also our guide on what Microsoft Intune is for context.
What Is an Intune Compliance Policy?
A compliance policy is a set of rules and settings that specify the minimum security requirements for a device. When a device checks in with Intune, the service evaluates it against the policy. Devices that meet all requirements receive a Compliant status. Those that fail receive Not compliant, which can trigger actions like sending an email notification, adding the device to a grace period, or blocking access via Conditional Access.
Common Compliance Settings by Platform
Windows Compliance Settings
- Minimum OS version — e.g., Windows 11 22H2 or later
- BitLocker encryption required
- Secure Boot enabled
- Antivirus and antispyware enabled and up to date
- Microsoft Defender Firewall active
- Password complexity and minimum length enforced
macOS Compliance Settings
- Minimum macOS version — e.g., macOS 14 (Sonoma)
- FileVault encryption required
- Firewall enabled
- Password required with minimum length and complexity
- System Integrity Protection enabled
iOS and iPadOS Compliance Settings
- Minimum iOS version
- Jailbreak detection — non-compliant if device appears jailbroken
- Passcode required with complexity settings
- Data encryption enforced
How to Create a Compliance Policy in Intune
- Open the Intune admin center at intune.microsoft.com
- Go to Devices → Compliance → Create policy
- Select the platform (Windows 10/11, macOS, iOS, Android)
- Name the policy and configure the compliance settings for your platform
- Under Actions for noncompliance, define what happens when a device fails — e.g., send an email after 1 day, mark as non-compliant immediately, or retire after 30 days
- Assign the policy to a user group or device group and click Save
Compliance Policies and Conditional Access
A compliance policy alone does not block access — it only sets the compliance state. To enforce access control, you need a Conditional Access policy in Entra ID that requires the device to be marked as compliant. Together, they form a powerful gate: only enrolled, compliant devices can reach corporate applications like Exchange Online, SharePoint, or Teams.
For macOS devices specifically, make sure the Mac is first enrolled before applying compliance policies. Follow our guide on how to enroll a Mac in Microsoft Intune before assigning compliance policies.
Compliance Policy Best Practices
- Start in report-only mode — evaluate the impact before enforcing, especially in mixed environments
- Use grace periods — give users time to remediate issues (e.g., 3 days) before blocking access
- Separate policies by platform — create distinct policies for Windows, macOS, iOS, and Android rather than one global policy
- Monitor compliance reports regularly — the Intune dashboard shows non-compliant devices and the reasons for failure
- Align with your security baseline — Microsoft publishes security baselines for Windows that you can import directly into Intune
For the full compliance settings reference, consult the Microsoft Intune compliance policy documentation.
📱 Need help deploying Microsoft Intune in your organization?
Our team handles Intune rollouts, compliance policies, and device enrollment for businesses. Book a free 30-minute call or drop us a quick message. 📅 Book a free 30-min call | 💬 Chat on WhatsApp
Compliance Policy Reporting and Remediation
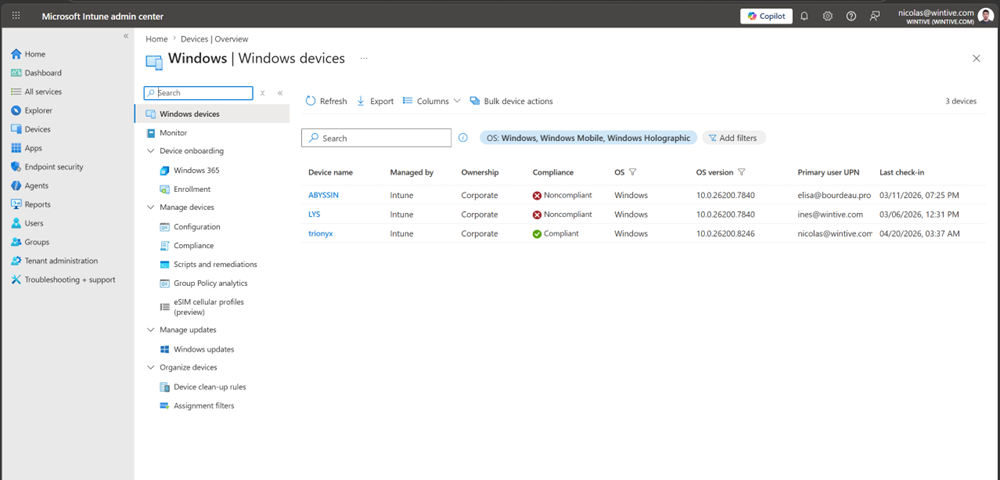
The Intune admin center provides a real-time compliance dashboard at Devices → Monitor → Device compliance. This report shows the percentage of compliant devices per platform, lists non-compliant devices with the specific settings they fail, and tracks compliance trends over time. For each non-compliant device, Intune shows the exact failed setting — for example, BitLocker is not enabled or OS version below minimum — which speeds up remediation significantly.
Combine compliance reporting with Conditional Access sign-in logs in Entra ID to understand which access requests are being blocked due to device non-compliance. For the full device management picture, see our guide on what Microsoft Intune is and how to enroll a Mac in Intune.