Microsoft Teams security and compliance is a critical responsibility for IT administrators. With Teams serving as the primary collaboration hub for most organizations, ensuring that meetings are recorded appropriately, data is protected, and users cannot leak sensitive information requires a layered approach. This guide covers the key Teams admin security settings, Microsoft Purview integration, and governance policies every IT admin should configure.
Teams security builds on Microsoft Entra ID Conditional Access and integrates with Microsoft Defender for Office 365. For the official Teams compliance documentation, see Microsoft’s Teams security and compliance overview.
External Access and Guest Access Controls
Specifically, two separate settings govern who can join Teams conversations from outside your organization:
- External access — allows users in other Microsoft 365 tenants to find, call, and chat with your users. Configure in Teams admin center → Users → External access. You can allow all external domains, block specific domains, or use an allowlist.
- For guest access — allows external individuals (with any email address) to join specific Teams and channels as guests. Configure under Teams admin center → Users → Guest access. Guests can be restricted from creating channels, sharing files, or chatting privately.
Meeting Security Policies
Administrators control meeting security in Teams through Meeting policies in the Teams admin center. Key settings include:
- Lobby bypass settings — configure whether external participants wait in the lobby or join directly. For sensitive meetings, require all external users to wait for admission.
- Auto-admission of people — control whether Teams admits guests automatically or requires manual approval from the organizer.
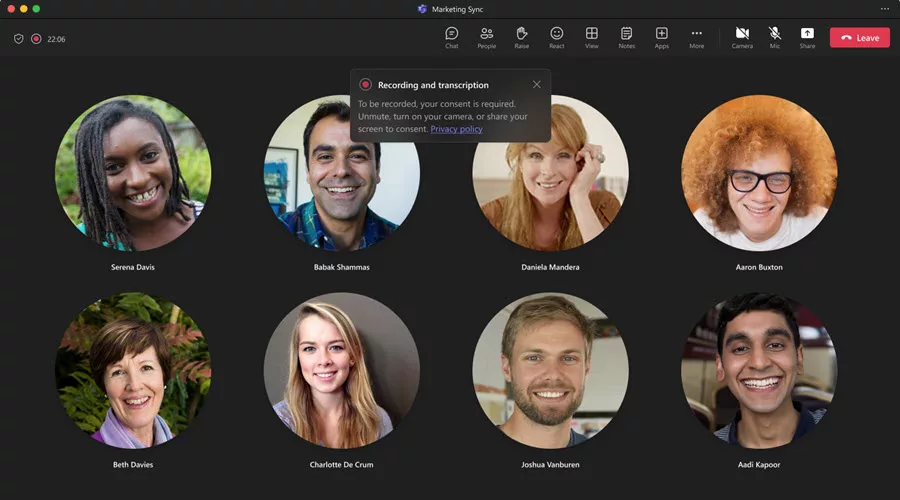
- Recording permissions — control which users can record meetings. Restrict recording to organizers only for sensitive departments.
- For end-to-end encryption (E2EE) — for one-to-one calls, enable E2EE to ensure content cannot be decrypted in transit. Note: E2EE disables transcription and recording.
Data Loss Prevention in Teams
Furthermore, Microsoft Purview Data Loss Prevention (DLP) policies apply to Teams chat and channel messages. In practice, a DLP policy detects and blocks messages containing credit card numbers, social security numbers, or custom sensitive information types before they reach recipients. To configure, open the Microsoft Purview compliance portal → Data loss prevention → Policies → include Teams chat and channel messages as a location.
Communication Compliance and Supervision
Microsoft Purview Communication Compliance monitors Teams messages for policy violations — offensive language, sensitive information disclosures, insider threats, or regulatory requirement breaches. Policies scan all Teams messages or target specific users and groups. Reviewers receive alerts when the system detects violations, and all evidence persists in a tamper-proof audit trail. Note that this feature requires a Microsoft 365 E5 Compliance add-on.
Domain Impersonation Protection
Notably, Microsoft Teams now includes Tenant-Owned Domain Impersonation Protection for external messages. When an external sender’s display name or domain resembles your organization’s domain, Teams flags the message and alerts the recipient. As a result, this protects against social engineering attacks where attackers impersonate internal addresses from an external account. Importantly, the feature activates automatically for enterprise tenants with no admin configuration required.
See also our guide on Teams app permissions and policies and our overview of Teams for business success.
📱 Looking to deploy or optimize Microsoft Teams in your organization?
From Teams Phone to Copilot rollouts, we help IT teams and managers get the most out of Microsoft Teams. Book a call or message us on WhatsApp. 📅 Book a free 30-min call | 💬 Chat on WhatsApp
Retention Policies for Teams
Additionally, Microsoft Purview retention policies apply to Teams chat messages and channel posts independently. Configure them in the Purview compliance portal → Data lifecycle management → Retention policies. You can retain Teams messages for a defined period (e.g., 7 years for regulated industries) and automatically delete them afterward. Importantly, Teams messages are stored in Exchange Online mailboxes and SharePoint — retention policies must cover both locations to be comprehensive. Users do not see a notification when messages are under retention.
Sensitivity Labels in Teams
Consequently, sensitivity labels from Microsoft Purview apply directly to Teams teams and meetings. Labeling a team as Confidential automatically enforces guest access restrictions, external sharing settings, and conditional access policies. In addition, meeting organizers can apply sensitivity labels to individual meetings, controlling who can join, whether recording is allowed, and whether the lobby is enforced. Configure sensitivity labels in the Purview compliance portal and publish them via label policies. For broader Entra ID governance and Teams deployment best practices, see our dedicated guides.

